U.S. Standards
- CCSS-Math: MP.1
- CCSS-ELA: 6-8.RST.3, 6-8.RST.4, 6-8.RST.7
- CSTA: 2-CS-01, 2-CS-02, 2-CS-03, 3A-CS-03, 3A-DA-09, 3B-CS-02, 2-AP-11, 2-AP-13, 2-AP-15, 2-AP-17, 3A-AP-17, 3A-AP-22, 3B-AP-09, 3B-AP-11, 3B-AP-21, 3B-AP-22, 3B-AP-23
- CS CA: 6-8.AP.11, 6-8.AP.13, 6-8.AP.15, 6-8.AP.16, 6-8.AP.17
- ISTE: 1.c, 1.d, 4.d, 5.c, 5.d, 6.b
U.K. Standards
Key stage 2
Pupils should be taught to:- design, write and debug programs that accomplish specific goals, including controlling or simulating physical systems; solve problems by decomposing them into smaller parts
- use logical reasoning to explain how some simple algorithms work and to detect and correct errors in algorithms and programs
- understand computer networks, including the internet; how they can provide multiple services, such as the World Wide Web, and the opportunities they offer for communication and collaboration
- use technology safely, respectfully and responsibly; recognise acceptable/unacceptable behaviour; identify a range of ways to report concerns about content and contact
Key stage 3
Pupils should be taught to:- undertake creative projects that involve selecting, using, and combining multiple applications, preferably across a range of devices, to achieve challenging goals, including collecting and analysing data and meeting the needs of known users
- create, reuse, revise and repurpose digital artefacts for a given audience, with attention to trustworthiness, design and usability
- understand a range of ways to use technology safely, respectfully, responsibly and securely, including protecting their online identity and privacy; recognise inappropriate content, contact and conduct, and know how to report concerns
Description
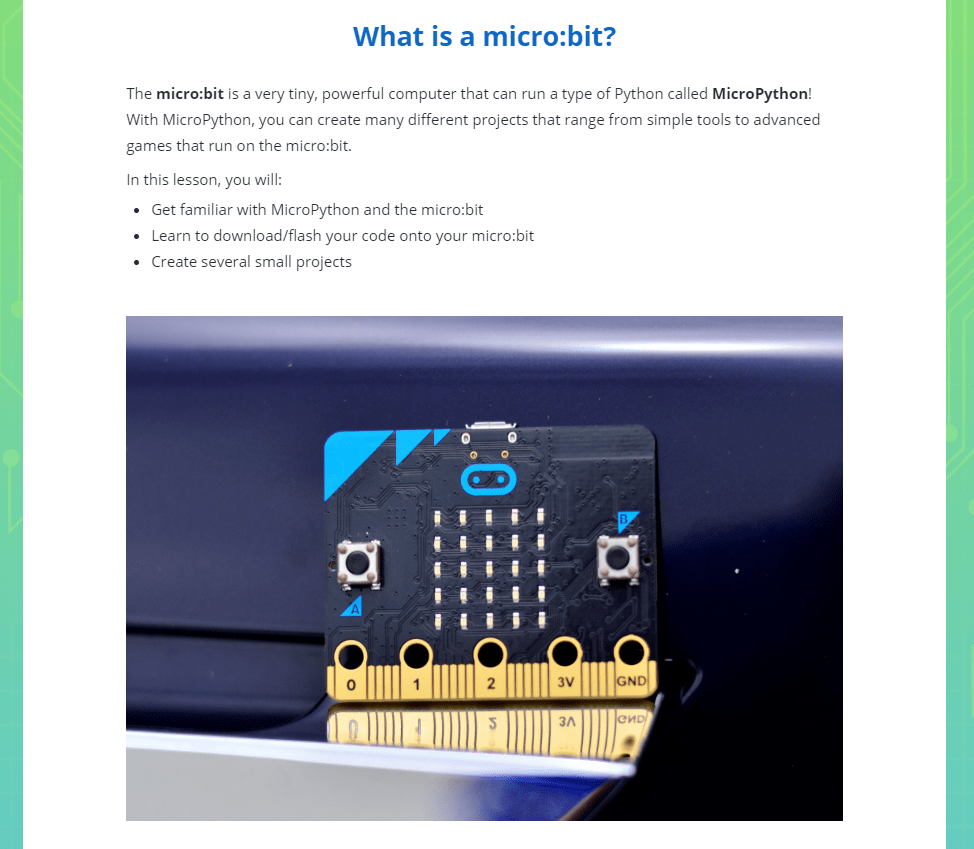
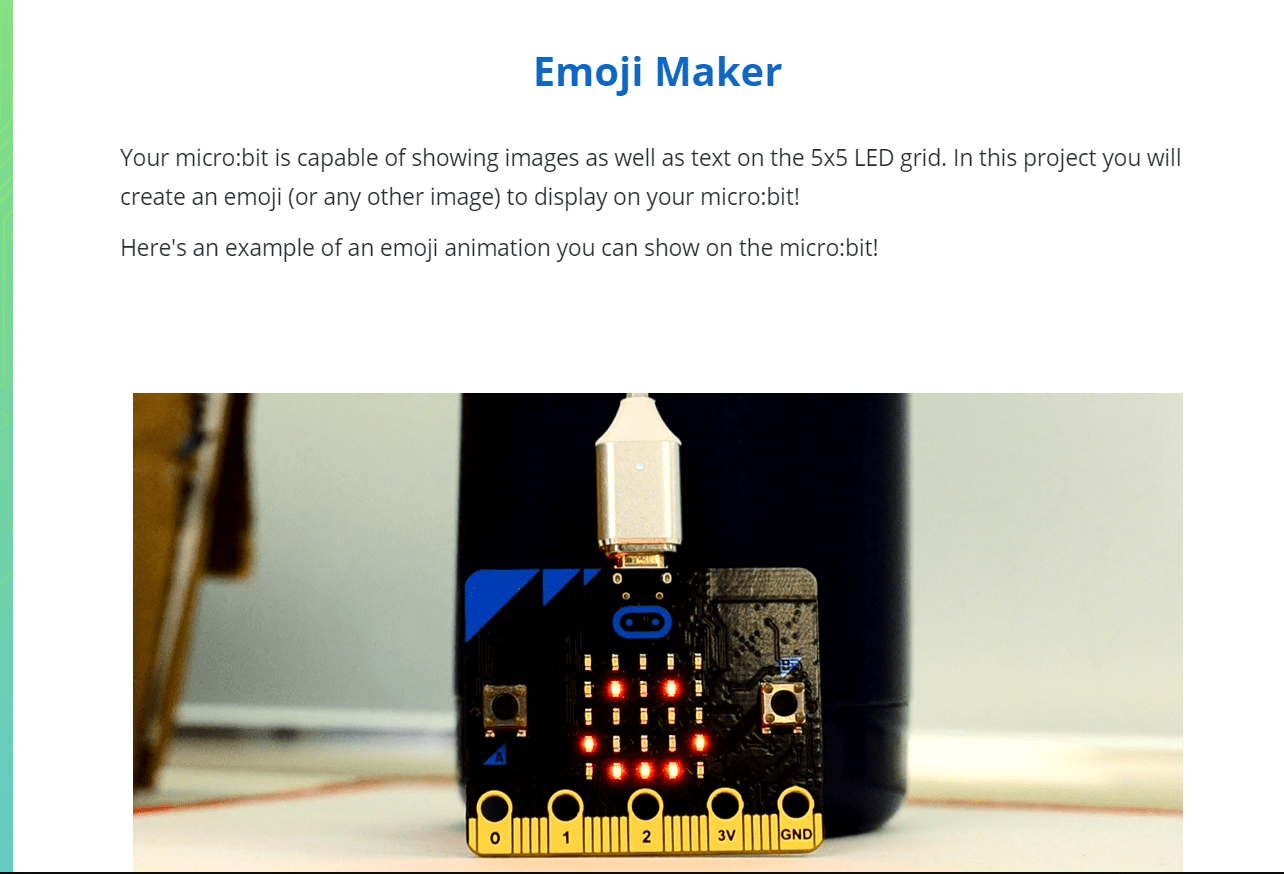
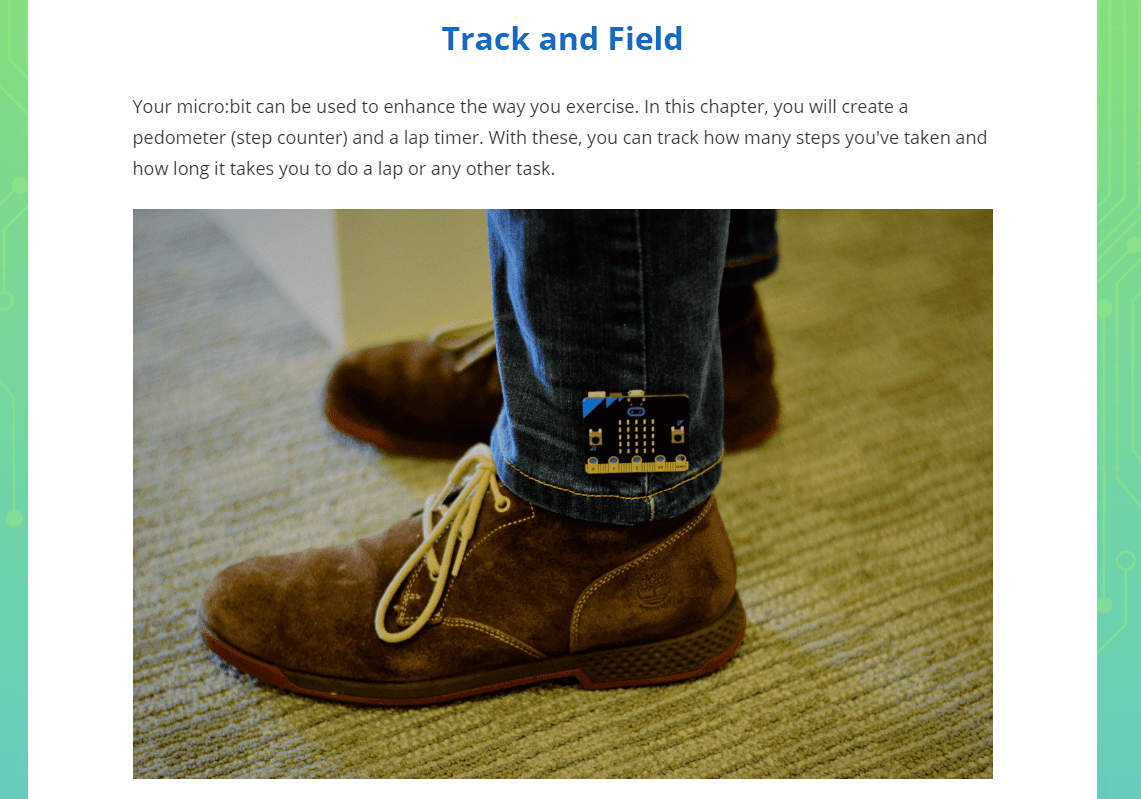
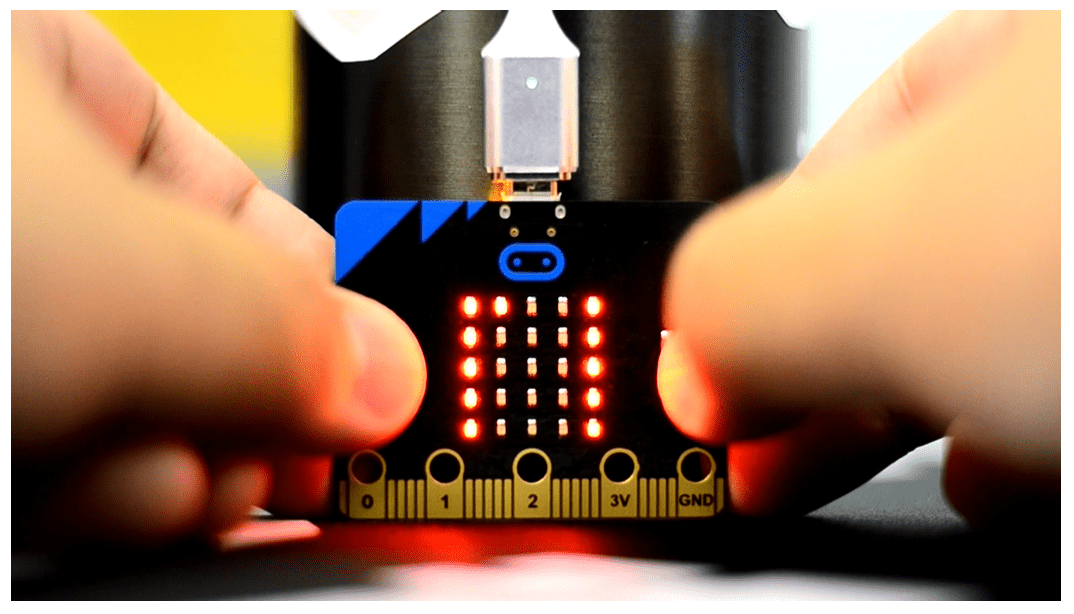
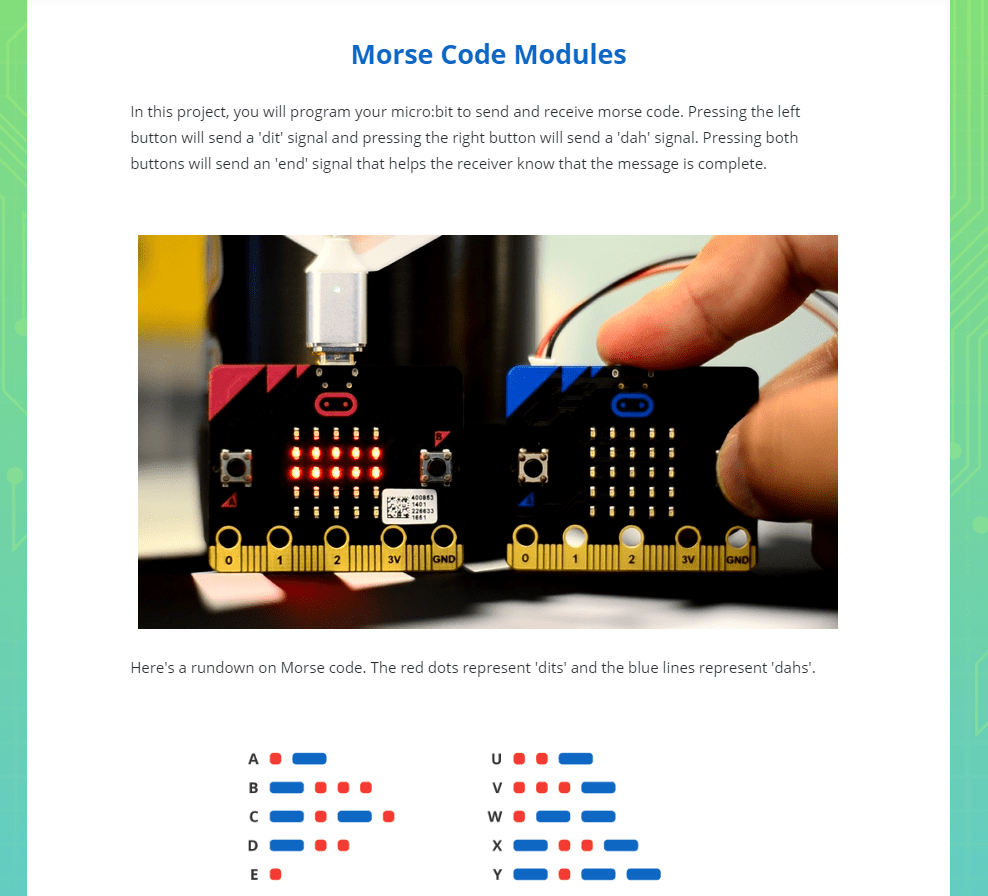
Introduce your class to physical computing with micro:bit and MicroPython. This course is an advanced introduction to micro:bit and requires prior Python programming knowledge. The curriculum engages students as they see their abstract programs come to life on a tangible physical device that they can control with their hands. Using built-in micro:bit sensors, buttons, and the 5X5 LED display, students build animated LED emojis, real-world temperature sensors, pedometers, multiplayer games, and even a two-way Morse code radio.
The course includes 16 hands-on projects with step-by-step instructions. It is delivered in an interactive notebook-style lesson format so that students can learn new concepts, write programs, and deploy code to the micro:bit right from the lesson interface. There is nothing to download or install on your computer. In addition, students can also launch Tynker Code Editor and write their own programs from scratch.
The lesson plans in this course build and reinforce STEM skills, problem solving, debugging, and collaboration skills, as students bridge digital and physical learning. Students will apply abstract programming concepts to create tangible hands-on micro:bit-based inventions.
Each lesson is designed for a class period of 45-60 minutes. All student work is automatically tracked and assessed, and you'll be able to monitor individual progress and mastery charts for your students.
This course is recommended for advanced students who are already familiar with Python. Beginner students may enroll in micro:Bit 101 where they use Tynker Blocks to program micro:bit.
This course is supported online and not supported on iPad.
Recommended Accessories: This course requires micro:bit devices (not included). You may purchase these separately at a variety of resellers. Each lesson has a detailed Parts List.
- micro:bit, USB cable, Battery pack, 2xAAA batteries (for each student or group)
- Accessories: Lessons 13, 14 require a Piezo speaker and Alligator clips
- Lessons 15,16 require two or more micro:bits
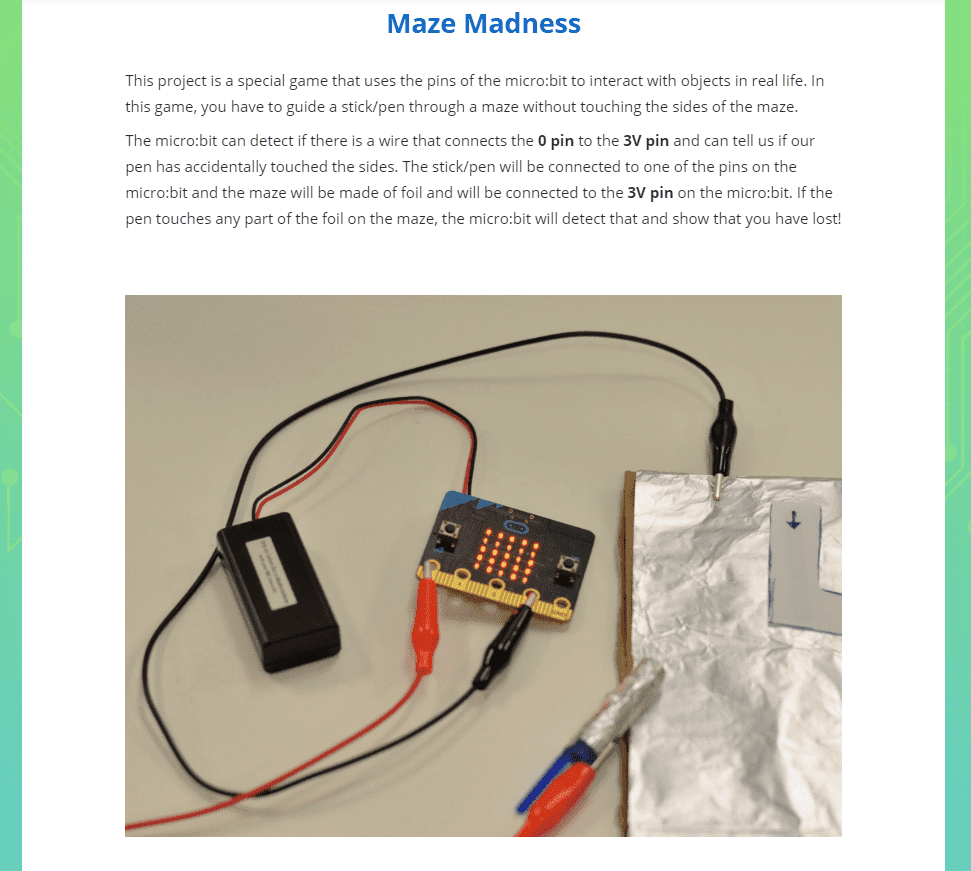
While most lessons need a single micro:bit, it is encouraged that students improvise to create inventions that incorporate external cables, LEDs, speakers, aluminum foil, and other accessories, when available.
See the this section on the micro:bit foundation for more ideas!
Topics
- micro:bit Python commands
- 2-way radio communication
- Deploying code to the micro:bit
- Light and temperature sensing
- Reading sensor values
- Gestures and motion detection
- Programming the LED grid
- Multiplayer game development
What Students Learn
- Display animations on the micro:bit LED
- Create classic arcade games on the micro:bit
- Create a pedometer by detecting steps
- Build a prime number checker
- Program a loaded die that always rolls 6
- Detect button clicks and other events
- Create multiplayer games using the radio
- Build a soundboard to play musical notes
- Extend the project to the physical world
Technical Requirements
* Online courses require a modern desktop computer, laptop computer, Chromebook, or Netbook with Internet access and a Chrome (29+), Firefox (30+), Safari (7+), or Edge (20+) browser. No downloads required.
Lesson
14 : Treasure Hunt
MicroPython 101
Time: 45+ minutes
Introduction
Code Introduced
Vocabulary
Objectives
Materials
Warm-Up (5 minutes)
Activities (45 minutes)
Facilitate as students complete all Treasure Hunt modules on their own:
1. Treasure Hunt (Document)2. Project 1: The 'Treasure' micro:bit (DIY)
3. Project 2: The 'Treasure Hunter' micro:bits (DIY)
4. Playing the Game (DIY)
5. Review
6. Quiz (Multiple-choice)